The recent cyberhacking attacks on Sony, CentCom and a number of well known companies over the past few years (especially Home Depot and Target) highlight a major development in the online world known as cyberwarfare. Cyberwarfare is defined as offensive and defensive measures designed to achieve superiority of control of cyberspace (Internet, networks, software and hardware) or parts thereof.
Although cyberwarfare is often thought of as an activity practiced by the state, attacks against corporations and the theft of credit card data can also be considered attacks against state sovereignty and symbols of statehood, and, hence, cyberwarfare. The information released in the Sony attacks, despite it being a foreign company, largely pertained to American operations and that bastion of Americana, Hollywood. Especially as it was an American subsidiary, Sony Pictures Entertainment, based in Culver City, Ca. And of course governments can, and do, invoke such attacks as justification for new cyber crime laws, some of them pretty restrictive.
Nevertheless, it may be useful to distinguish types of cyberwarfare, or to permit that some forms of cyberwarfare (offensive or defensive) may be more easily carried out by states. An attack on the electrical power grid may be considered cyberwarfare while the theft of corporate credit card numbers may better be considered hacking. Nevertheless the line is hazy (and there is of course a long-standing form of warfare known as economic warfare).
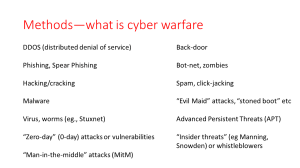
Here are some forms of cyberwarfare I identified for my political geography class last fall.
There are undoubtedly others and the definition is flexible enough to include “insider threats,” or those who work from within (the Sony attacks have often been attributed to insiders, although the US government has consistently maintained that North Korea is ultimately responsible.). Some of these are well-known, such as Zero-day capabilities (so called because they been worked on for zero days) and “advanced persistent threats” (APT) a euphemism for government-sponsored attacks (usually from China, the world’s most persistent source of cyber attacks, along with…. the USA).
There are some interesting geographies of cyberwarfare, including:
–who is the target of attacks (who is vulnerable)
–who is perpetrating attacks
–differential effects of attacks, including collateral damage
In my class, I suggested that we could understand cyber vulnerability as occurring at geostrategic chokepoints where the cables that carry the bulk of internet traffic come to shore. If you like, this is the new geopolitical map after Mackinder, where who controls the cables controls the global flows of traffic!
Norse, which has been the most widely quoted source of doubts about North Korea being responsible for the Sony hack, have a very nice dynamic map of live attacks here. It nicely illustrates some of the geographies involved (click map below). (They use the “honeypot” system of offering faked targets that attract attacks. For example they may have a site which looks like an unsecured piece of factory control software, or a computer without a firewall. According to their website, they have over 8 million honeypots scattered around the world.)
Chokepoints are also critical for surveillance, which is why GCHQ and NSA have programs to tap into them. Skewjack Farms near Bude in Cornwall is one such site, and some of its operations have been revealed by Channel 4 (UK) using Snowden documents.
But there are other geographies too, as this graphic about the now well-known Stuxnet infection demonstrates:
Although Stuxnet targeted the Iranian enrichment plant at Natanz by the Bush and Obama administrations in conjunction with Israel, a programming error let the virus into the wild, where it infected over 100,000 hosts in more than 155 countries, especially Indonesia, India, and Azerbaijan. This creates a new geography of collateral war damage from cyber operations.
Although geographers have not looked into these geographies all that much (Derek Gregory has glossed on Stuxnet [Update see also “Geography, Territory and Sovereignty in Cyber Warfare” by David Midson, and “Wikileaks and the Global Geography of Cyberwarfare” by Gastón Gordillo), a new paper by Robert Kaiser in this month’s issue of Political Geography attempts to document what he calls the “birth of cyberwar.” Kaiser chooses the 2007 cyber attacks on Estonia as his beginning point that galvanized western security concerns, so much so that he claims it served to elevate cyberwarfare to the same risk levels as terrorism itself. (Russia is usually held responsible for the Estonian attacks, mostly consisting of DDoS or distributed denial of service using botnets.) Certainly after this we see the US Cyber Command being established (June 2009) headquartered at Fort Meade, home to the NSA. (DIRNSA is also DIR USCYBERCOM.) However, the latter also has origins in US military’s pre-existing planned or operational cyber operations, and the command is actually a subunit of US StratCom. Additionally, its mission states states that it will only defend DoD computers and networks (not commercial).

Kaiser’s paper does raise some good issues, whether or not his chosen event is the “birth” of cyberwarfare. (Cyber attacks are known since at least the early 1980s, when the CIA placed a “logic bomb” that blew up a Soviet gas pipeline–see Thomas Reed, At the Abyss: An Insider’s History of the Cold War, p. 269). Operation Merlin, recounted in James Risen’s great 2006 book State of War may also count, although it is not strictly speaking a primarily cyber event (the CIA planned to leak doctored nuclear blueprints to Iran) but rather a Stuxnet precursor (Stuxnet being perhaps the most famous single cyberattack to date, and is surprisingly not mentioned by Kaiser).
One issue that doesn’t get mentioned by Kaiser deserves much more attention, and that is the geographies of encryption, which I’ve written about at length before. I was going to say more here, but this blog post is already pretty long, sorry ¯\_(ツ)_/¯
Suffice it to say then that I don’t think you can understand cyberwarfare without involving encryption, and in fact to some extent they overlap. Cyber vulnerabilities are in part encryption vulnerabilities. And cyber defenses are also in part about encryption. The “end-to-end” encryption that David Cameron is proposing to take away (or ban) would remove protections on privacy and increase security vulnerabilities, nicely illustrating that all these issues are bound together. So we really need to be talking about a material assemblage of cyberwarfare/encryption/privacy/security together.
While Kaiser is right to highlight cyberwarfare and help geographers start working on it, his article shows how far we have to go (indeed his article is not really about cyberwarfare, but more about what he calls discursive aporias of imagineering about cyberwarfare, or more plainly the ways the Estonian event was dealt with in terms of policy enactment). He is also pretty skeptical about deterring cyber attacks, which is hard to square with the fact that thousands of attacks are prevented every day. And yes of course there are fear mongers and exaggerations by security companies with things to sell you, but there are also other security experts out there and usable estimates of damage.
Still, as they say in footie, we’re off the mark and hopefully we can kick on from here.




Reblogged this on Rashid's Blog.
Reblogged this on OromianEconomist and commented:
‘Cyberwarfare is defined as offensive and defensive measures designed to achieve superiority of control of cyberspace (Internet, networks, software and hardware) or parts thereof. Although cyberwarfare is often thought of as an activity practiced by the state, attacks against corporations and the theft of credit card data can also be considered attacks against state sovereignty and symbols of statehood, and, hence, cyberwarfare.’